Vulnerability status
Vulnerability status is shown in the vulnerabilities grid and can be any of the statuses shown in this table. You can edit the vulnerability status.
Status | When to set this status |
|---|---|
Reported | This is the default status of a vulnerability after it is discovered by Contrast. The vulnerability in this application could possibly be exploited. |
Confirmed | Confirm that the vulnerability is a true finding by reviewing the source code or exploiting it. |
Suspicious | The vulnerability appears to be a true finding based on the details provided, but requires more investigation to determine its validity. |
Not a problem | The vulnerability is being accounted for without any source code changes. To set this status, you must select one of these reasons. Vulnerabilities set to this status will not revert back to Reported if found again.
|
Remediated | The vulnerability has been fixed by changing source code or config files within the application. |
Fixed | The vulnerability has been fixed by changing the source code or because of a reason given under the Not a problem status. A vulnerability set to this status will not revert back to Reported if found again. Required permissions:
|
Remediated-Auto-verified | This status can only be automatically set. (It can't be manually set by a user.) If a vulnerability is not reported within the time limit set in the vulnerability policy, it will automatically be set to Remediated-auto-verified. |
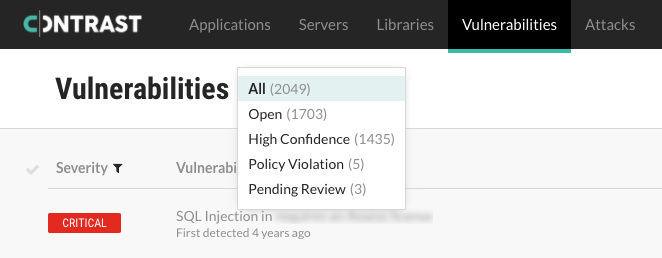
Policies that are set to Reported, Confirmed, Suspicious are considered to be open. Policies that are set to Not a problem, Remediated, Fixed, or Remediated-Auto-verified are considered to be closed. You can filter vulnerabilities by Open to see only open statuses, or by All to see both open and closed statuses.
If the agent reports a vulnerability and Contrast has never seen it before, Contrast creates a new entry for the vulnerability. If that vulnerability already exists, Contrast updates the existing entry, issue count and number of days since it was last detected. All vulnerabilities will be reopened with the same pre-existing status, except those that were previously set to Remediated or Remediated-Auto-verified. Those will be reopened as Reported.