Analyze runtime library usage
Runtime library usage gives insight into which parts of a library are used by your applications, which can reduce investigation time for CVEs by showing how much a library impacts your application. This also improves collaboration because security teams can confirm with development teams that an application uses a vulnerable library at runtime.
Note
Only organizations with a Contrast SCA license can see full usage details. To learn more, contact our sales department at sales@contrastsecurity.com.
Select Libraries in the header, click Runtime and view the Usage column to see if, and how much, a library is used at runtime. The usage number represents the number of items used by any instrumented applications, out of the total number of items known to be available in that library.
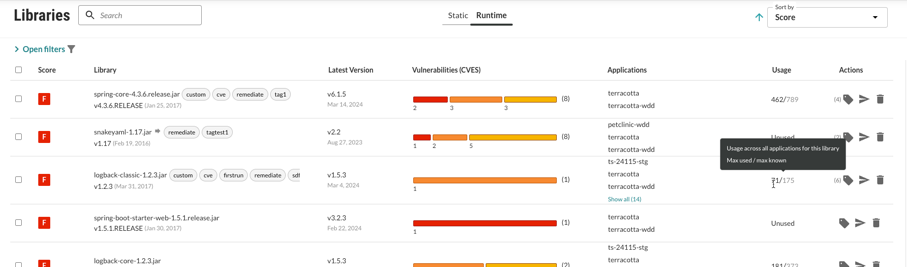
Items loaded may be classes, files, or functions, depending on the languages of the applications using this library. If a primary application contains multiple applications that use the same library, the classes loaded will be representative of each merge application.
When an application uses a library, the Contrast agent reports the items loaded within the library. As the application uses more items within a library, usage counts increase in Contrast.
If you have the appropriate license, you can also view full library usage details for a particular application:
Under Applications, select a specific application to see the details view.
Select the Libraries tab for the application.
Select the usage counts for a specific library. This opens an overview and usage panel.
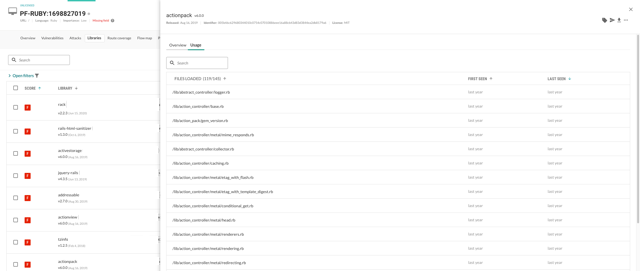
Click the Usage tab to view each class, file, or function used. Click the search icon
to search for specific classes. You will also see the first time and last time Contrast observed it in use. Library exports will also include full usage data. Click the Overview tab to view What happened (describes the issue(s)), as well as What’s the risk (lists the Severity badge, CVSS Score, CVE title, and policy violations).
Note
For a merged application, Contrast will report when a class was first seen and last seen for all applications it contains within the corresponding Last Seen and First Seen columns.
Click the More menu (
) to view package details, repository location, delete the library, or export usage details in CSV format.
Select the X to close the details panel.