Set modes for CVE shields
Instead of detecting categories of attacks, CVE shields defend specific CVEs in applications from attacks.
Set one of the following modes for applications hosted on servers running in a Development, QA, or Production environment:
Off: This mode disables the CVE shield entirely.
Monitor: In this mode, the CVE shield identifies and reports attacks.
Monitor at perimeter In this mode, the CVE shield tries to identify and report a possible attack before the application can process it. This option is not available for all CVE shields.
Block: In this mode, the CVE shield identifies, reports, and blocks attacks.
Required: Check that you have Organization or Rules Admin permissions.
Check that settings for servers hosting your applications are configured to use the correct environments.
To view CVE Shields.
From the user menu, select Policy management.
Select CVE shields. and select the name of a CVE shield.
To find a specific CVE shield, enter a partial or full name in the search box.
To set the mode for all or multiple applications:
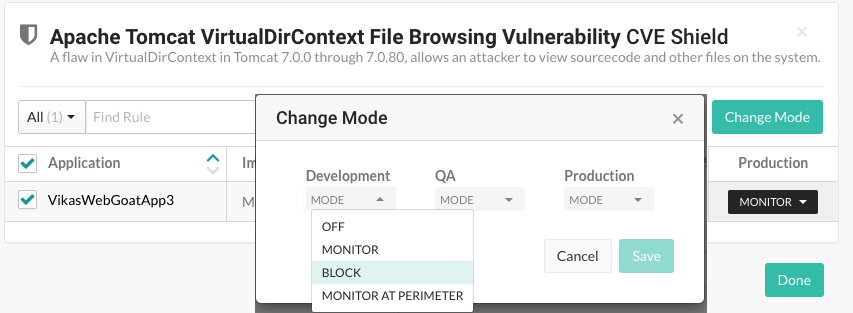
To select all applications, select the Application checkbox. To select multiple applications, select the checkbox for each application.
Click Change mode.
In the Change Mode window, select the CVE shield mode for the selected applications in a one or more environments.
Click Done.
To set the mode for a single application:
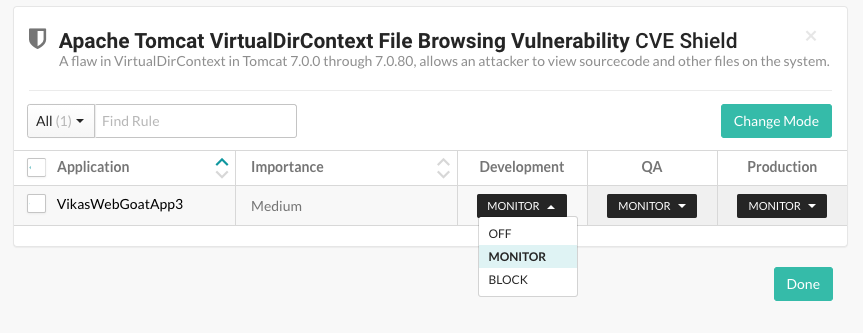
At the end of the row for an application, select the menu in an environment column.
If an environment is not defined for the server hosting the application, when you hover on that environment, a tooltip appears. To configure the server for that environment, click Set up and select the settings icon (
 ) at the end of the server row.
) at the end of the server row.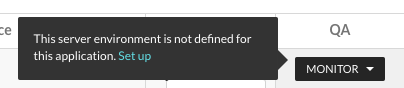
Select a CVE shield mode for the application in the selected environment.
Select Done.