Export vulnerability findings
To export vulnerability details:
Select Vulnerabilties in the header, then use the check marks in the left column of the vulnerabilities grid to select the vulnerability or vulnerabilities you want to use for the export.
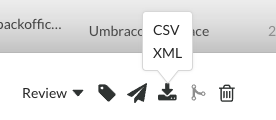
In the batch action menu that appears at the bottom of the page, select the Export icon, then select the format you want to use for the export (CSV or XML).
Contrast begins to export the data.
Check the Notifications panel (
 ) to see when the export is completed. The notification contains a link for you to download the exported data.
) to see when the export is completed. The notification contains a link for you to download the exported data.Exports contain the following information for each vulnerability:
Vulnerability Name
Vulnerability ID
Category
Rule Name
Severity
Status
Number of Events
First Seen
Last Seen
Application Name
Application ID
Application Code
Primary Application Name
This column shows the name of a primary application for a merged application.
CWE ID
Request Method
Request Port
Request Protocol
Request Version
Request URI
Request Qs
Request Body
Instance ID
Tip
To create more complex custom software composition analysis reports about your applications, you can use the Application API to access Contrast vulnerability data.
You may also explore additional details on your vulnerabilities using a manual method.
For, example, this curl request retrieves a list of vulnerabilities that also shows a list of the applications in which each vulnerability was found. The jq tool formats the data as CSV for use in a custom report.
curl \
-H "Authorization: $(echo -n $username:$servicekey | base64)" \
-H "API-Key: $apikey" \
https://app.contrastsecurity.com/Contrast/api/ng/$orgid/orgtraces/filter?expand=request | \
jq -r '.traces[] | {uuid: .uuid, protocol: .request.protocol} | [.uuid, .protocol] | @csv'